Alternative Images also known as Any-Image
By default TrinityX comes bundled with playbooks for conventional HPC but also AI based workloads for the various distributions including Ubuntu and OpenSUSE. See the general information for detailed information regarding these playbooks. However, in some occasions a different distribution release is preferred.
TrinityX supports what we call the Any-Image approach. Besides the out-of-the-box provided playbooks, which technically already utilize the Any-Image functionality, it allows building alternative images to a higher degree, to e.g. have a Rocky-8 image, while the headnode runs a different distribution, for example Alma-9.
Any-Image supports four approaches. Default where the base is generated based on the controller's distribution. A 'base' approach where a pre-packaged base image is used to build further on top of, and a 'docker' approach where Docker images found on the Docker hub repository are used to provide a base. The official Docker images are tested but the stack is prepared to handle custom Docker images as well. And lastly, added in TrinityX 15.3, an osgrab approach where an already installed node can be grabbed and turned into a TrinityX image.
Refer to the recipes to see examples on how to utilize the Any-Image functionality.
How it all works
Creating images is split in two main steps, image-create and image-setup. Image-create creates the image as the name implies. It bootstraps the OS, installs required packages and sets it up to be a minimal Luna bootable image. Image-setup is similar to controller.yml, a playbook that sets up TrinityX inside the image.
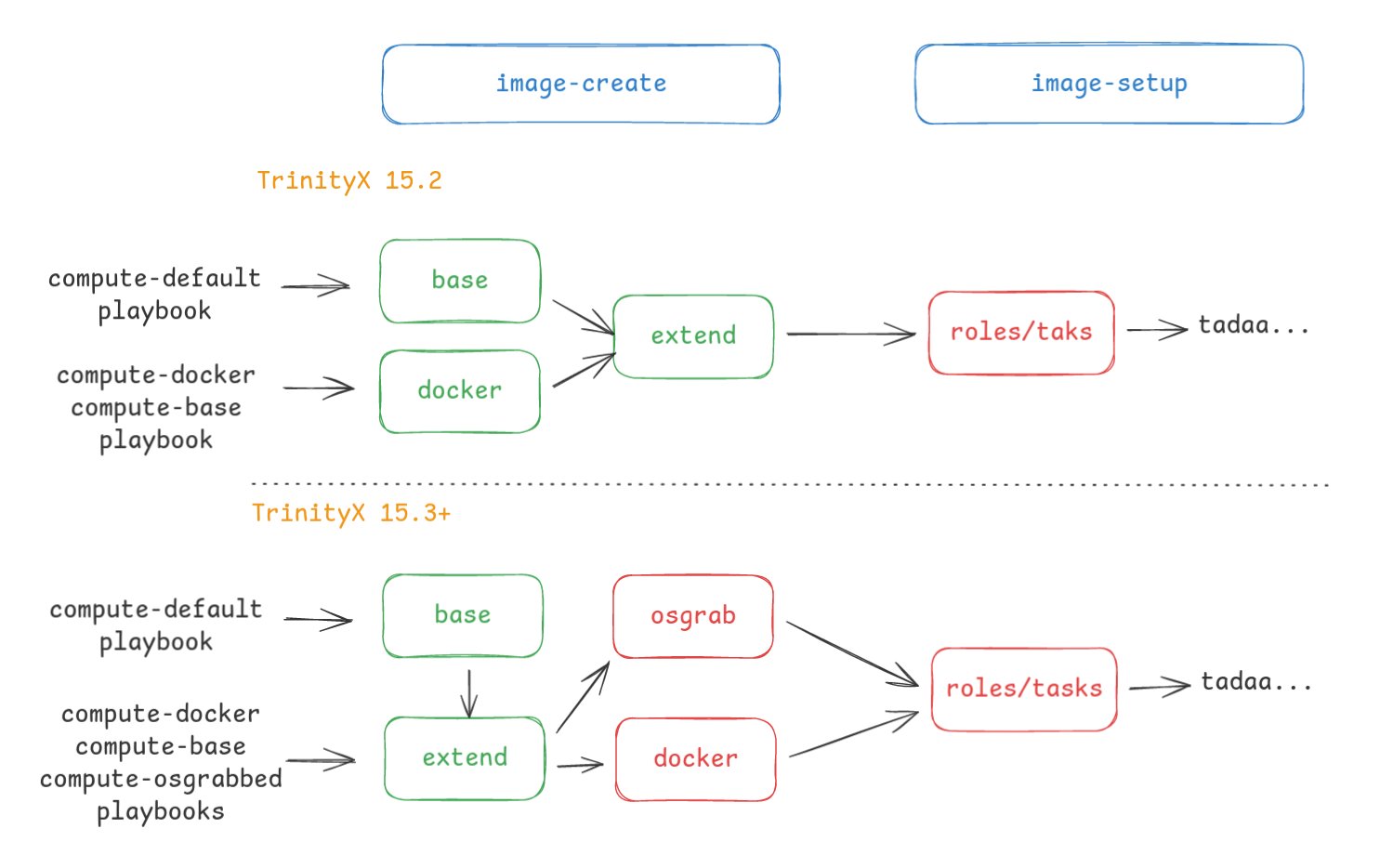
In image-create we identify four parts:
- Base: bootstraps the OS.
- Extend: configures the image to be a minimal luna bootable image.
- OSgrab: ensures the installation of missing packages.
- Docker: converts a docker container into an image. Ensures the installation of missing packages.
The main difference between TrinityX 15.2 and 15.3 is the way how packages are managed, utilizing OSgrab and Docker steps. These now typically run inside a chrooted environment, ensuring correct package installation (read: using the image local repositories). In the above diagram, parts that run inside a chrooted environment are red color highlighted.
Tested Matrix
The matrix below presents the combinations tested and confirmed working.
x86_64
| distribution | base | docker | osgrab |
|---|---|---|---|
| Rocky 8 | Rocky-8, Rocky-8.9 | rockylinux:8, rockylinux:8.9 | ✅ |
| Rocky 9 | Rocky-9, Rocky-9.3 | rockylinux:9, rockylinux:9.3 | ✅ |
| Alma 8 | - | almalinux:8, almalinux:8.10 | ✅ |
| Alma 9 | Alma-9, Alma-9.4 | almalinux:9, almalinux:9.6 | ✅ |
| Ubuntu | Ubuntu-22, Ubuntu-24 | ubuntu:22, ubuntu:24 | ✅ |
| OpenSuse | OpenSuse-15, OpenSuse-15.5 | - | |
| Centos 8 | Centos-8 | - | |
| Centos 9 | Centos-9 | - | |
| RedHat 8 | - | - | ✅ |
| RedHat 9 | - | - | ✅ |
aarch64
| distribution | base | docker | osgrab |
|---|---|---|---|
| Rocky 9 | Rocky-9, Rocky-9.5 | - | ✅ |
| Ubuntu | Ubuntu-22 | - | ✅ |
| OpenSuse | OpenSuse-15, OpenSuse-15.5 | - | ✅ |
EL10 based images note
Due to a too big (version) difference between Ansible and Python provided by EL9 versus EL10 distributions, it is not possible at the time of writing to build EL10 based images on an EL8 or EL9 based controller or vice versa.Workarounds are being evaluated and are expected to be released in the near future
External links
Docker official provided images repositories: